What a Threat Assessment Actually Is: A Guide for Family Office Advisers
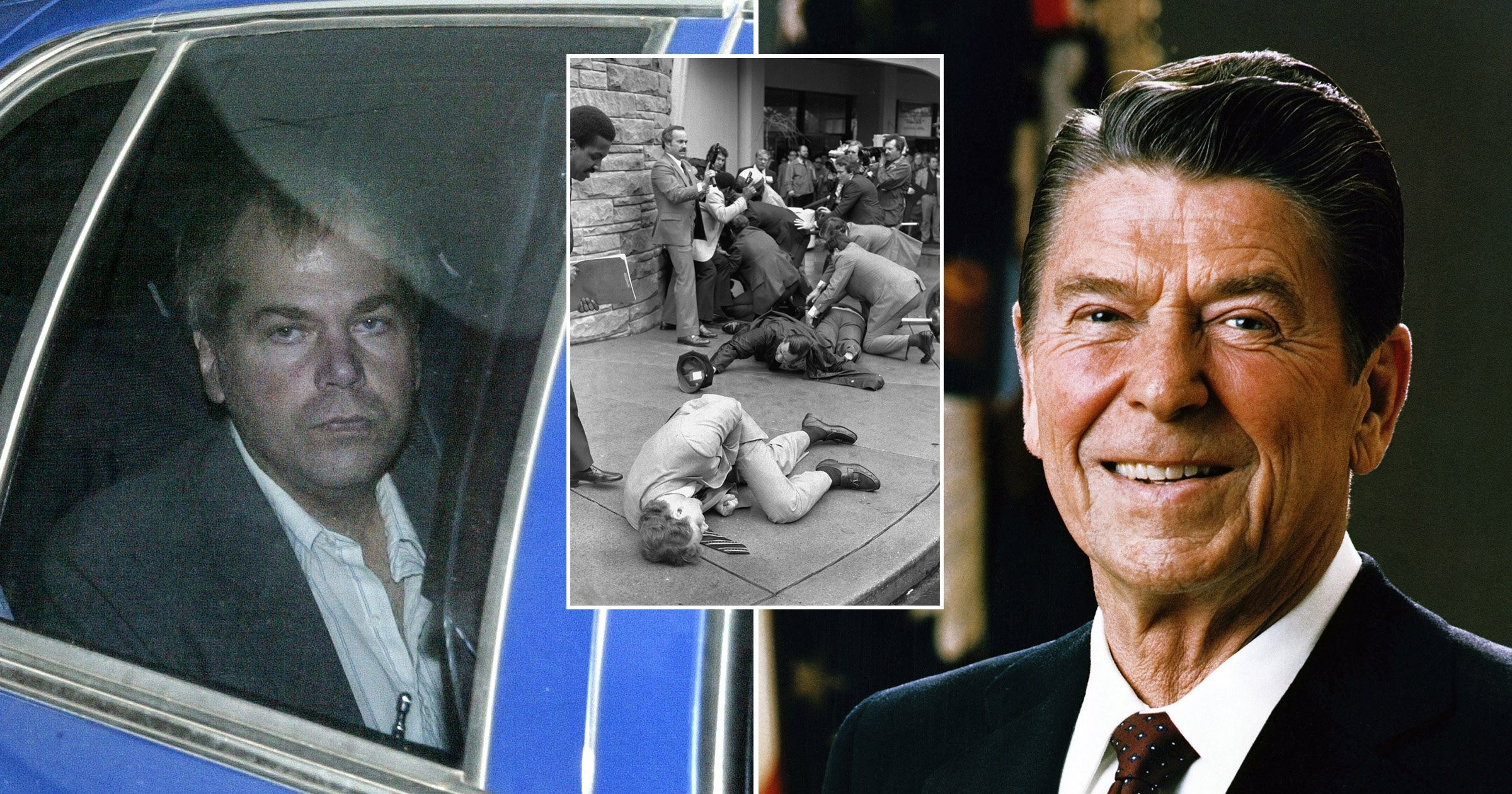
📍 On the 30th of March 1981, John Hinckley Jr. shot President Ronald Reagan outside the Washington Hilton hotel.
Hinckley was not an invisible, unknowable attacker who appeared from nowhere. He was, in retrospect, exactly the kind of individual a properly trained threat assessment practitioner would have identified and flagged long before he pulled the trigger.
He had developed a dangerous fixation on actress Jodie Foster, one that had escalated from admiration into something far more purposeful. He had acquired weapons. He had stalked Foster at Yale University. He had written letters explaining his intentions in considerable detail. He had travelled to locations where the President would be present, rehearsing proximity and access.
⚠️ Every one of those behaviours, read together by someone who understood what they were looking at, told a clear and progressive story.
❗ The failure was not a lack of information. The information was there. The failure was a lack of structured interpretation, an inability to read the pattern of behaviour for what it was.
That gap is precisely what modern behavioural threat assessment was designed to close. And the word that matters most in that sentence is not “assessment”, it is “designed.”
🛡️ Behavioural threat assessment and management is a preventive discipline. Not predictive, nobody can tell you with certainty that a specific individual will act. But preventive, identifying the build-up of risk early enough to intervene before harm occurs.
That distinction is fundamental. Prediction is a claim about the future. Prevention is a commitment to acting on what is visible right now.
🔁 Most security responses are reactive. Something happens, and a team is mobilised.
Behavioural threat assessment works entirely the other way around. It looks for the pattern before the event, the fixation, the planning, the escalation, and intervenes at the point where intervention is still possible, still proportionate, and still calm.
💡 That is not a philosophical difference. It is the difference between stopping and responding.
🎯 What a threat assessment does
🚫 A threat assessment is not a personality judgement.
🚫 It is not a psychiatric diagnosis.
🚫 It is not a red, amber or green label attached to a concerning message and filed away.
✔️ It is a structured, evidence-based process for assessing whether a person of concern is moving towards targeted harm, based on their behaviour, communications, motives, capabilities, and the changing pattern over time.
In plain terms, we are looking for evidence that a person of concern exists in the first place, then investigating them.
Not waiting for a threat to land in an inbox.
Not monitoring a dashboard.
🔎 Actively looking for the individual who may be moving towards harm, identifying who they are and what they are doing, and building an evidence-based picture of where they currently sit on the pathway.
That investigative mindset is what separates genuine threat assessment from threat monitoring, and it is the difference between getting ahead of a situation and simply reacting to one.
📚 That approach is grounded in the research tradition established by the US Secret Service, whose Exceptional Case Study Project examined 83 individuals known to have attacked or attempted to attack prominent public figures over the past 50 years.
The central finding was unambiguous.
⚠️ Targeted attacks are the product of organised thinking and behaviour.
⚠️ The attacker has a motive, has selected a target for a reason and has moved through a recognisable behavioural sequence before acting.
I was mentored directly by Dr Robert Fein, co-author of that landmark study, and that research shapes everything I do in this work.
⚖️ Actions speak louder than words
This is where most threat management arrangements fall short, and it is worth being direct about it.
⚠️ Most security providers focus heavily on communications.
- Threatening emails are flagged
- Abusive messages are logged
- Social media is monitored
And whilst all of that has a place, it represents a dangerously incomplete picture of the actual risk.
📌 A threatening communication is just one behaviour. One data point among many.
The old adage that actions speak louder than words has never been more relevant than in threat assessment, because the individuals who pose the greatest risk are often the ones saying the least.
Hinckley’s letters were significant, but they were not the whole story.
👉 It was his actions, the stalking, the weapons acquisition, the travel, the rehearsal, that mapped his true trajectory.
Had anyone been looking at the full behavioural picture rather than focusing solely on his communications, the pathway would have been unmistakable.
⚠️ In a significant number of cases involving serious, premeditated harm, direct threats are absent altogether.
The person planning to act has little incentive to warn their target.
What they do instead is follow a pattern that researcher Reid Meloy, whose work I have had the privilege of discussing directly on The Defuse Podcast, has described with considerable precision:
- fixation that intensifies over time
- escalating planning activity
- acquisition of information or weapons
- attempts to get closer to the target
- ultimately a point at which violence feels like the only remaining option
📈 Meloy describes these as warning behaviours, dynamic, escalating indicators that signal increasing risk and demand an operational response.
They are not dramatic in isolation.
❗ Taken together, by someone trained to read them, they are unmistakable.
The pathway was there in Hinckley’s case. It is there in most cases.
👉 The question is always whether anyone is looking at the right things.
🧭 What this means in practice
A proper threat assessment asks a specific set of questions:
- Is this person moving along a pathway from grievance towards action?
- Is the behaviour escalating?
- Do they see violence as a solution to their problem?
- Do they have the means, the access and the resolve to act?
Those questions apply equally whether the subject of concern is a fixated individual targeting a prominent person, a former employee nursing a grievance or an organised group treating a family member as a point of leverage.
🔄 Critically, the assessment looks in two directions simultaneously:
- Outward at the person of concern, their behaviour, their escalation, their proximity to action
- Inward at the client, their vulnerabilities, their routines and the gaps in their current arrangements that a targeted approach might exploit
⚠️ Assessment without management, however, is only half the job.
Once the picture is built, the response should be proportionate, early, and intelligence-led.
Sometimes that involves close protection.
More often, it involves changes to routine, reduced digital exposure, legal intervention, or a welfare approach to the person of concern.
The right response depends entirely on what the assessment found.
🚨 Most serious threats do not come out of nowhere
They are built over time, through behaviour, in plain sight.
🎯 The job is to find the person of concern, investigate them thoroughly and act early enough that the response remains calm and proportionate, well before the situation demands something more urgent than a conversation.
📞 If you want to take this further
For advisers who want to understand how behavioural threat assessment fits within a properly structured, layered security plan — and how to implement these processes for the clients you work with — I would welcome that conversation directly.
These discussions are confidential, carry no obligation and are more straightforward than you might expect.
📱 Call +44 (0)207 293 0932
📧 email [email protected]
🌐 visit www.defuseglobal.com